Pretty much similar to the term terrorism, any attempt to destroy and damage a property or digital technology is called cyberterrorism. It is targeted towards various entities, such as governments, private infrastructure, and people of a particular region, to cause disruption and havoc.
At the same time, digital data, an important asset in the modern world, can be targeted with minimal knowledge by hackers. These attempts are rising at an alarming rate with enhanced cyber-terrorism tactics and techniques. This article briefly discusses cyberterrorism including response strategies. Dive in to understand more.
In recent times, attacks have increased to a significant level since getting access to the internet and content that teaches people how to misuse it in the dark web cybercrime websites is available at large. This led to the instigating idea amongst criminals to conduct cyberterrorism, without getting caught and inflicted in the process.
Tactics of Cyberterrorism
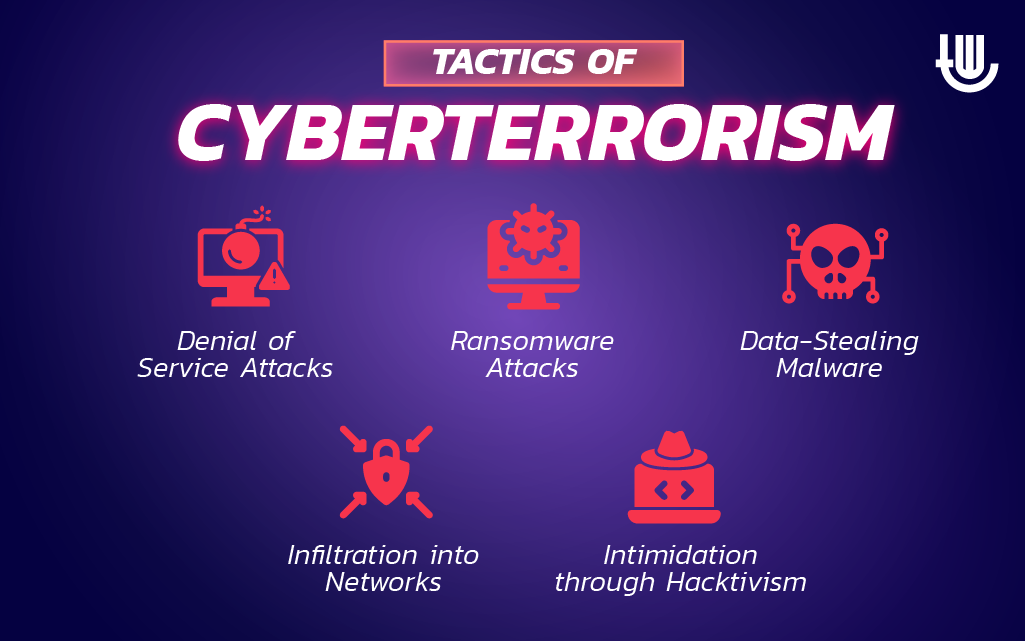
To understand the superficial level of threats or a generic overview, we will see the common tactics involved in cyberterrorism.
Denial of Service Attacks:
This type of attack occurs when the entire digital infrastructure is made unresponsive or denied of its usual service. A common way is by sending a large number of requests, also known as packet flooding.
Ransomware Attacks:
Ransomware attacks are when an entire digital infrastructure is infected with a specific type of malware that prevents users from accessing it. This malware changes the extension of sensitive files, rendering it useless.
Delivery of Data-Stealing Malware:
Different types of malware are meant to harm computers and associated devices. Some trojans can secretly stay in a computer without being detected and steal data such as passwords, card details, and even typed content in real-time—this benefits cyberterrorism by gathering sensitive data and inflicting more harm by exploiting it.
Infiltration into Networks:
When a server or device is left insecure, it gives a doorway for cybercriminals to stay in the system, move toward other devices, and damage them. Once inside a network, the attacker can stay persistently, encrypt data, steal data, or shut it off permanently.
Intimidation through Hacktivism:
For geopolitical and personal propaganda, cyberterrorism can take the form of hacktivism, where an individual or group of hackers can collectively damage common people or government assets. This is the latest and widely emerging threat to the country’s smooth digital operations.
Techniques of Cyberterrorism

Malware Spreading:
Various malware are meant to harm the devices and possibly cause a catastrophe in the smooth functioning of systems. They are sent as email attachments, website links, fake software, or spam.
Port Flooding:
This is a classic method of denial of service attacks when open and internet-accessible ports are overwhelmed with huge traffic. This makes the services unavailable to legitimate users. Various tools are exploited by cybercriminals that are often found for free on the internet.
Defacement:
Defacement normally occurs on websites powered with CMS systems such as WordPress, Joomla, etc. When a hosting provider’s credentials are compromised, criminals can upload malicious and misleading web pages and host them as a part of your websites. To see if your website is compromised or not, check this site.
Zero-day Attacks:
Zero-day attacks are exploited wildly across the world but do not have a security patch yet. Mass attacks are carried out against the technologies vulnerable to zero-day attacks, especially public-facing or country-sensitive assets such as power grids, electricity units, IoT devices, etc.
Phishing:
To target the masses of a country or a region, criminals often host websites that look like exact replicas of big brands and fool their visitors with harmful intentions. They might ask users to log in, download malicious files, deposit money, or share sensitive information, which can help attackers conduct their cybercrime plan’s next move.
Data Breaches and Broking:
Once inside the network, cybercriminals can attempt to extort the information, leading to data theft. This data is advertised on the dark web for profit, which can interest other criminals for various reasons.
Response Strategies for Cyberterrorism
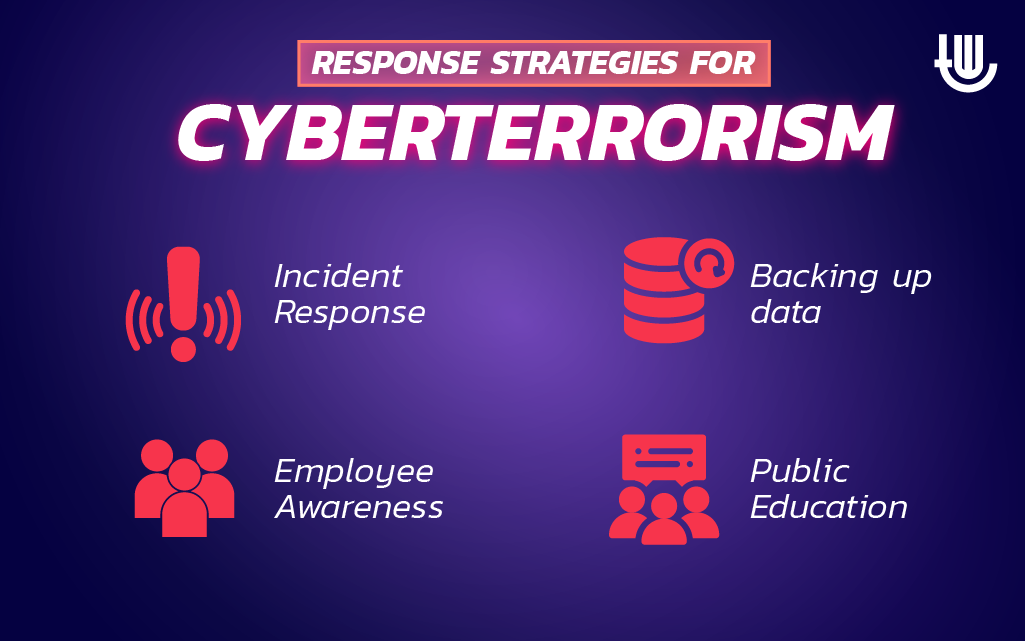
Staying informed about the latest tactics, techniques, and response strategies is essential for protecting critical infrastructure, sensitive data, and our way of life. Let’s look at some response strategies to prevent any hazard from cyberterrorism.
Incident Response:
A good incident response plan that covers all possible attack scenarios and reduces the time to recover from the threat is mandatory for public and private organizations. Since cyber threats are increasing daily in every aspect, such as numbers and advances, having a well-documented plan for mitigations and actions is necessary.
Backing up Data:
Some ransomware attacks can be avoided by ensuring a backup for all the encrypted data. Also, making data available in the event of any calamities inside and outside human control is essential and can be availed with backups.
Employee Awareness:
Exploiting human mindset and gaining a strong foothold in the systems by leveraging human errors, insecure passwords, default credentials, and social engineering are basic ways most cyberterrorism attacks are conducted. Thus, employee awareness is an important element when considering a wholesome cybersecurity plan.
Public Education:
The government should ensure that the latest techniques are relayed to the masses so that they can learn how to protect themselves, which is critical for building a more resilient online environment. One such initiative by the Indian government is about the CSK and various tools to eliminate viruses in the devices, which are available to all users.
Wrapping Up the Topic:
Cyberterrorism is a complex subject with layers of technical, geopolitical, and psychological elements. Cybercriminals are motivated by various reasons, such as extremist views, political movements, financial gains, geographical feuds, etc. Their understanding is to cause chaos on a large level where their existence and attempts can be seen as a dangerous threat.
Thus, the best we can do as individuals, organizations, or governments is to ensure that safety measures are known and implemented. I hope you liked our article on cyberterrorism tactics, techniques, and response strategies. Let us know your views in the comments.

Author Bio:
This article has been written by Rishika Desai, B.Tech Computer Engineering graduate with 9.57 CGPA from Vishwakarma Institute of Information Technology (VIIT), Pune. Currently works as Cyber Threat Researcher at CloudSEK. She is a good dancer, poet and a writer. Animal love engulfs her heart and content writing comprises her present. You can follow Rishika on Twitter at @ich_rish99.