Your device is prone to cyberattacks if you do not take enough care of it. Hackers, being technologically advanced, can access your systems remotely and can manipulate them. Network thieves also can intercept your data when it is sent over an insecure network. These are some of the common ways that tell how vulnerable your information is on the Internet.

What happens if the endpoint devices are hacked?
If your endpoint devices are hacked or if someone with malicious intents manages to access it, then the following risks are associated:
- An attacker can access and view your sensitive files and might steal the data that belongs to your workplace.
- He might install a backdoor on your devices, allowing him to skip the password process of authentication and still be able to access it anytime.
- He might delete all the sensitive files of yours, causing a major data loss if you don’t regularly back up your files.
- He might also change your account’s password and other credentials or view your stored account password in the browser cache. This allows him to potentially lock you out of all the arrangements with stored personally identifiable information such as credit card details.
Ten tips to keep your endpoint devices and data safe in day to day life
#1. Never set the same password for two accounts.
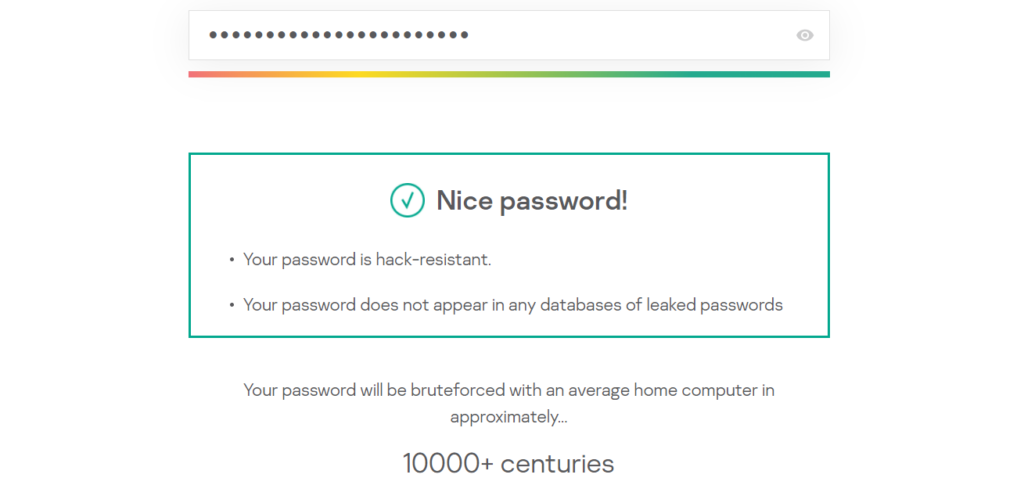
Having the same password for two or more accounts is dangerous because one account’s compromise will also lead to the other. Besides, it is also advised to avoid keeping a weakly configured password on for any login process. You can check the strength of the password here. Also, always check the time required to crack your password if it is attacked by the brute-forcing method.
#2. Surf without being tracked using VPN.
Having a VPN forges your real IP and covers your trail for online internet activities. Because of this, it is easier to stay hidden and be traced over the Internet. Simple websites such as Who.is and Shodan.io reveal a lot of information about your device and user. Thus, I’d always recommend to use proxies and VPN facilities and escape from the eyes of a hacker.
#3. Avoid clicking on pop-ups that come with attractive offers.
Pop-ups are the easiest ways through which a hacker puts a malicious code into your system. These pieces of code are functional so that they bypass the security system and attack as per their programming specifications. They are known as worms, trojans, malware, and viruses in layman’s terms. So it is best recommended to avoid browsing the sites that have a lot of pop-ups because even a single click on such websites is dangerous.

#4. Do not use apps that ask for unnecessary permissions.
All the app-stores don’t verify the type of application it is putting for users to download. Also, not all apps come from trusted developers. Thus, they might ask to access unnecessary permissions that might not be needed for the app to function. Thus, deny using such apps that ask you for irrelevant permissions to work.
#5. Make sure that you don’t download attachments from unknown sources.
Sending infected files through email attachments is one of the most common ways of harming the victim’s endpoint device. So whenever you’re expecting an email, do verify from the source about the authenticity of the attachments. In this way, you’ll be sure that there are no harmful files in your system.
#6. Buy premium plans of endpoint-security tools to avail of additional features.
Premium plans come with additional features such as data privacy and extra layers of protection of most devices. They also help in detection, prevention, and keeping statistics of the anomalies that occurred in your systems over the past few days. Thus, premium plans also come with automated patching so that you can sit back and let the system auto-heal.
#7. Avoid connecting to public sources of the Internet.
Public Internet sources, such as WiFi and hotspots, are malicious hackers to broadcast viruses and connect with victims. It is possible to gain access to the victim’s devices and intercept the data being sent through the internet connection. Although most of the websites send encrypted forms of data, it is possible on certain websites that lack such means of protection.
#8. Always send your emails and messages in an encrypted format.
There are various ways to exchange emails other than the most commonly known to ensure data safety. One such resource uses those emails that allow you to set a decryption key to the end-user to view the message. Your day to day email software also allows you to choose encrypted versions of mails. Besides, the newer software helps to authenticate the user using the public key decryption methods. This, in turn, allows us to verify the sender.

#9. Always use a VirtualBox for testing harmful environments.
Certain software can ruin your main system if it malfunctions or shows unexpected behavior. At such times, we can use the virtualization of systems to install a system within a system. Even if a system crashes due to any software environment, it can keep your device configurations intact. Also, before running any software environment, it is always advised to keep a backup of the sensitive data to retrieve it anytime.
#10. Regularly check your devices.
Lastly, you know your devices the best. Always keep an eye on any malicious behavior that never happened before. Keep a check what files are causing your devices to show abrupt behavioral changes and check if they contain any anomalies. It is always required to scan your devices from time to time and detect the problems before becoming a hazard.
Conclusion
As we conclude, these were the ten tips to keep your endpoint devices and data safe in day to day life. These practices are easy to implement and provide security in the times of cyberattacks.
Knowing that many working professionals carry certain organization-specific sensitive data and protecting them should be the topmost priority. Thus, a few steps of caution aided with automated tools and scanners can make your devices hack-proof. So wait no more, and start implementing them right away.

Author Bio: This article has been written by Rishika Desai, B.Tech Computer Engineering Student at Vishwakarma Institute of Information Technology (VIIT), Pune. She is a good dancer, poet and a writer. Animal love engulfs her heart and content writing comprises her present. You can follow Rishika on Twitter @ich_rish99.